Ongoing Threat: PostgreSQL Instances Under Attack
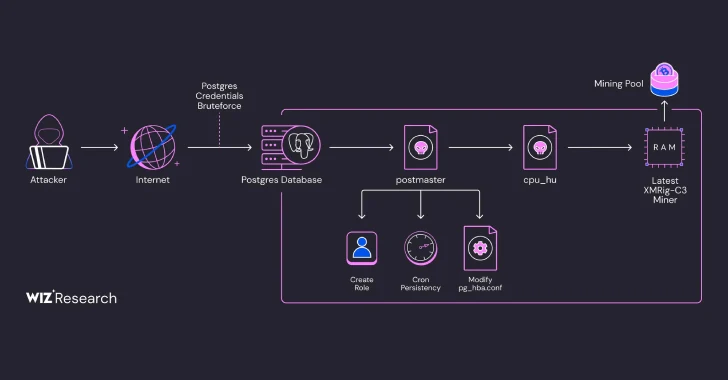
Exposed PostgreSQL servers have become the latest target of a fileless cryptocurrency mining campaign, aiming to gain unauthorized access and deploy mining malware.
Attack Attribution and Evolution
Cloud security firm Wiz attributes this activity to a threat actor tracked as JINX-0126, first identified by Aqua Security in August 2024. The malware strain involved, known as PG_MEM, has since evolved to incorporate advanced evasion techniques:
- Unique Hash Per Target – Binaries are generated with a distinct hash per system, making detection based on file hash reputation ineffective.
- Fileless Execution – The miner payload runs directly in memory, bypassing traditional endpoint security solutions that rely on static analysis.
Exploiting PostgreSQL Weaknesses
Security researchers estimate that over 1,500 PostgreSQL instances have been compromised due to weak or predictable credentials. The attack hinges on abusing the COPY … FROM PROGRAM SQL command, which allows direct execution of shell commands on the host machine.
Attack Sequence and Payload Deployment
- Initial Access – Attackers exploit misconfigured PostgreSQL services to execute arbitrary shell commands.
- Reconnaissance & Persistence – A Base64-encoded shell script is deployed to kill competing miners and drop a malicious binary named PG_CORE.
- Obfuscation Tactics – An additional Golang binary (codenamed postmaster) mimics the PostgreSQL database server, helping maintain persistence via cron jobs and elevated privileges.
- Fileless Mining Execution – The malware downloads another binary (cpu_hu), which retrieves and executes XMRig, a Monero mining software, directly in memory using the memfd technique.
Scale and Impact of the Attack
Security analysts discovered that each compromised machine is assigned a unique mining worker ID. Three different cryptocurrency wallets associated with the campaign have been identified, each containing approximately 550 workers, indicating that over 1,500 systems have likely been hijacked.
Mitigating the PostgreSQL Cryptojacking Threat
Organizations using PostgreSQL should take immediate action to secure their databases against such threats:
- Enforce Strong Authentication – Use robust passwords and disable default or weak credentials.
- Restrict Network Exposure – Limit public accessibility of PostgreSQL instances and implement firewall rules.
- Monitor for Unusual Activity – Set up alerts for suspicious queries, such as unexpected COPY … FROM PROGRAM executions.
- Implement Cloud Security Solutions – Utilize Cloud Workload Protection Platforms (CWPPs) with behavior-based detection to counter fileless threats.
This attack highlights the growing sophistication of cryptojacking campaigns, reinforcing the need for proactive cloud security measures to safeguard PostgreSQL and other exposed assets from cybercriminals.